Just 5 Minutes to My 2nd Stored XSS on Edmodo.com

How I Found the Bug
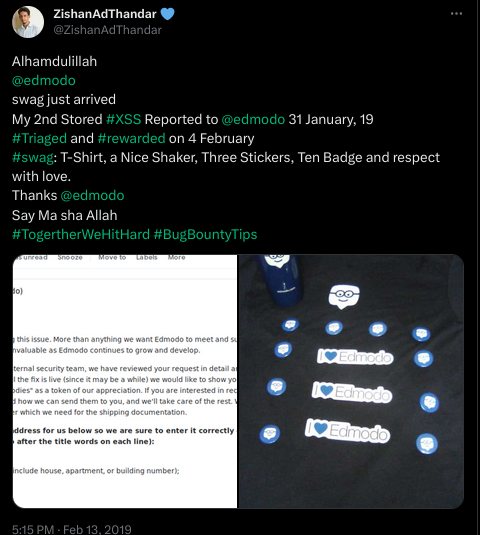
My overall experience with Edmodo has been excellent. They provide:
- ⚡ Quick responses to security reports
- 🎁 Cool swag (just look at that haul!)
- 🔍 Lots of input fields to test (perfect for hunters)
The Accidental Discovery
This time, it wasn’t planned. I was bouncing between different bug bounty programs when I decided to check Edmodo again.
Suddenly, I noticed something different - I was redirected to new.edmodo.com. A new subdomain means new attack surface! 🎯
The Testing Process
- Posted my XSS polyglot on new school creation
- Tested the poll feature with various payloads
- Clicked my profile picture - redirected to
www.edmodo.com/* - Noticed notifications on this domain
- Clicked a notification and… BOOM! 💥
The Vulnerability
The notification system wasn’t sanitizing user input. When I clicked on a notification containing my payload, it executed in the context of www.edmodo.com.
💡 Key Takeaway: Always test notification systems, profile views, and cross-subdomain interactions!
Key Takeaways for Bug Hunters
- Test new subdomains immediately - new.edmodo.com led to this find
- Don’t ignore notification features - they often handle user input poorly
- Cross-subdomain testing - my payload worked across different edmodo domains
- Re-use successful payloads - that same polyglot worked twice!
Video Proof of Concept
Twitter Status
Timeline
- 🐛 XSS Reported to Edmodo on 31st January, 2019
- ✅ Triaged and rewarded on 4th February, 2019
- 🎁 Swag received on 13th February, 2019