Hunting methodology and experience of my First Stored XSS on Edmodo.com
- What is my methodology?
- How I got the bug?
- How I got the payload?
- Twitter Status
- Video Proof of Concept
- Experience with Edmodo
- Timeline
There are many people sharing images of Edmodo swag. It looks cool and everyone says it’s a cross-site scripting bug. So, I assumed there were lots of XSS vulnerabilities. Edmodo is a very secure platform and they take security seriously, so I decided to hunt.
Even elite hunter Prial Islam Khan shared an image of his Edmodo swag, which inspired me a lot.
So, I decided to test Edmodo. But I’m a newbie. How can I find the bug? If I can, that means anyone can!
What is my methodology
Is it simple steps or any l33t automation tool? Nope, it’s just manual… too manual.
As a newbie, I tried a very noob way to hunt: I filled all fields with XSS payloads, hoping to get a popup and cool swag ❤️.
How I got the bug
I filled every field with XSS payloads, hoping for a popup, but got nothing. But hope (and believe) is always with me.
I read Arbaz Hussain’s (@kiraak-boy) post, where he advised to give time to every program before losing hope.
📖 Recommended Reading:
10 Rules of Bug Bounty by Arbaz Hussain
So, I decided to start finding bugs on Edmodo subdomains. I used Sublist3r (coded by Ahmed Aboul-ela) to enumerate subdomains:
# Install Sublist3r
git clone https://github.com/aboul3la/Sublist3r.git
cd Sublist3r
pip install -r requirements.txt
# Find Edmodo subdomains
python sublist3r.py -d edmodo.com
🔗 Tool Link: Sublist3r on GitHub
Then? Then I just opened beta.edmodo.com and… BOOM! 💥 XSS popped! I started investigating and found the injection point was in the status post feature.
How I got the payload
People might be wondering about the payload I used. It’s not mine - I used an XSS polyglot crafted by the legendary Ashar Javed.
Here’s the payload I used:
">><marquee><img src=x onerror=confirm(1)></marquee>" ></plaintext\></|\><plaintext/onmouseover=prompt(1) ><script>prompt(1)</script>@gmail.com<isindex formaction=javascript:alert(/XSS/) type=submit>'-->" ></script><script>alert(1)</script>"><img/id="confirm( 1)"/alt="/"src="/"onerror=eval(id&%23x29;>'"><img src="http: //i.imgur.com/P8mL8.jpg">
💡 Note: I used this payload initially, then removed unnecessary parts while making the PoC video.
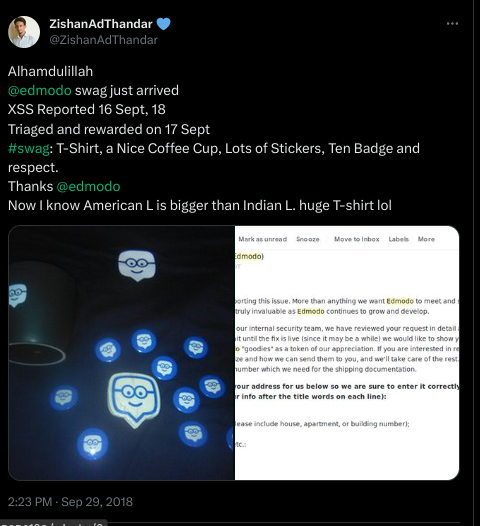
Twitter Status
🔗 Direct Link: View on X/Twitter
Experience with Edmodo
Edmodo is a very secure platform and they take security seriously. I had a great experience with their security team. Their response was quick and communication was clear.
Special thanks to Chip Benson and the entire Edmodo security team!
Video Proof of Concept
Check out the video PoC (and don’t forget to subscribe to my YouTube channel for updates!):
Timeline
- 🐛 XSS Reported to Edmodo on 16 September, 2018
- ✅ Triaged and rewarded on 17 September, 2018
- 🎁 Swag received on 29 September, 2018